Background
As security risk assessment and security risk management software, SECTARA (Risk Management Software Australia) was designed around the premise that, like us, subscribers to the system would be among some of the most security-conscious people on the INTERNET. As secure & fully encrypted software, security is thus a core tenet and design principle, and this is evident throughout SECTARA.
This is not only apparent in terms of our cybersecurity controls/protections, but also in the way that we’ve ensured that in-product rules and processes regard your sensitive data as the key asset, and prevent security risk assessment access to it from other users (and even us).
There are so many SaaS applications online these days that it’s hard to keep track – in many respects this is great news, but in terms of security, there are risks that must be managed. Caught up in the appeal that this new market and the capability that it offers, many subscribers fail to properly consider or examine the security credentials of the platforms on which they are sharing and storing their sensitive data.
________________________________________________________________
RELATED ARTICLES: How Security Risk Assessment Software Works | Benefits Of Collaborative & Easy-To-Use Security Risk Software | The Benefits Of Tailored & Scalable Risk Assessment Software | How To Maximise Productivity In A Security Risk Assessment | Demonstrated Value To Security Risk Stakeholders | The Benefits Of SECTARA’s Advanced & Intuitive Risk Assessment Methodologies
________________________________________________________________
The country in which data is stored, the manner in which it is sent and received (and to whom it is exchanged/shared with through integrations), and whether or not developers and administrators can gain access to your sensitive data, are some of the key issues that are being overlooked. For example, did you know that DropBox is a US-hosted entity? At least Microsoft and other large vendors have done something about it on their Office 365 platform, which is hosted within Australia and subject to local jurisdictional control.
Also, what do you know about the owners/developers/administrators of the platform that manage your data? In most cases they can access your data directly – who are they, and where do their loyalties lay? Have they even carried out a security risk assessment of their own platform? Do they even appreciate the importance of security risk management?
Why the Problem Exists
The vast bulk of software companies focus on capability first; after all, if the product doesn’t do what the target market wants, it won’t be successful. It appears that even the larger vendors adhere to this principle, as evidenced by the myriad of reported cyber exploits affecting major platforms over the years.
While security may be considered important, it doesn’t necessarily attract the attention that it deserves. Products are also not always being built by security experts, so the focus on capability first is reinforced, and very rarely are products both secure and fully encrypted.
Key SECTARA (risk management software Australia) Security Benefits
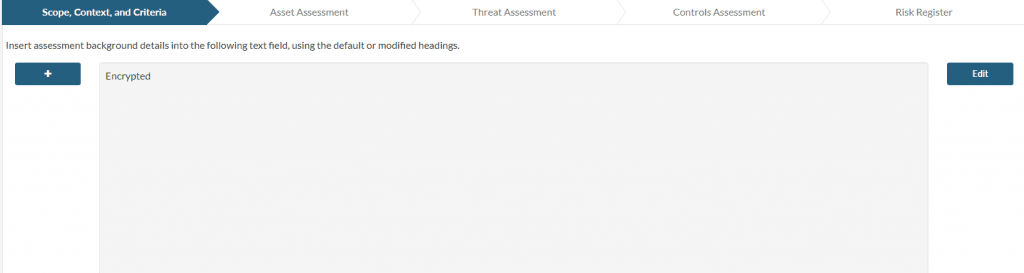
The effect of field-level encryption – only your account users can see your sensitive data
We built SECTARA with security risk management in mind; in fact security (risk assessment) is core business on the platform and our user-base, so it came before any other consideration. As a consequence, our subscribers enjoy a range of benefits that very few others can collectively lay claim to, including being:
- IRAP compliant – this means that we align ourselves with the most highly regarded benchmark for cybersecurity within the region. Similar in principle and design to NIST requirements in the US, the IRAP program is Australia’s premier cybersecurity program and control set. Having a Director/Head of Cybersecurity who is an IRAP consultant sets us apart in this regard.
- Hosted within a Government accredited data centre (which means that Government Agencies and Departments use the same environment). As such you can easily make the case that it’s fit to host your data.
- Encrypted at field-level, meaning that, no matter where your sensitive data is in the system at any given time, it is in encrypted form. That is, of course, with the exception of when it’s on your screen. What this further means is that neither us, or other 3rd parties can access this data, even if they were to be able to gain access to it.
- Equipped to enable you to create five user types, thus giving you major flexibility and control around who can access what.
- Controlled and managed by Government security cleared administrators (at SECRET and TOP SECRET levels). While this is unnecessary for most SECTARA purposes (unless we decide to move into a higher-level/accredited data environment in the future) it’s a by-product of the security risk management work that we do for Government. What it does give you, however, is as good an assurance as possible that the key people behind SECTARA have been found to be trustworthy enough to be granted access to some of the country’s most sensitive Official information.
- Data Residency: Per our product road map, we will develop regional and local data storage options for account holders. This means that you’ll be able to select where your data is stored from AWS locations around the world. Keep an eye on our updates for this.
All of this ultimately provides peace of mind and will allow many to overcome the concerns of internal IT Departments who are naturally cautious when approving external systems.
How to get started with SECTARA Risk Management Software Australia
If you see the same great benefits that we do in SECTARA, there are several methods to get started:
- Register for one of our Bronze, Silver or Gold Plans.
- Sign up to our absolutely Free Plan.
- Arrange an online demo.
- Contact us
As a valued subscriber, you will be comprehensively supported via our Ticketing System and Knowledge Base, and you can still always contact us direct when you need to. Best of all, all subscribers are entitled to a free copy of the Security Risk Management Aide-Memoire (SRMAM) when they register (applies to both free and paid plans). SRMAM was written by Julian Talbot, the original author of SRMBoK.
We look forward to seeing you on SECTARA!